
Secure services refer to managed cybersecurity solutions. These protect data, networks, and endpoints from threats. Common threats include ransomware and phishing attacks.
SMBs face big risks. In high-risk industries like manufacturing and finance, breaches hit hard. Stats show 43% of cyberattacks target small businesses. Average losses reach $25,000 per incident.
This article gives actionable steps. It helps implement secure services. You’ll get industry-specific checklists and ROI calculations. These beat basic guides online.
Identifying Your Security Vulnerabilities
Start with a self-audit. Check for weak spots in employee training. Look at password management too. Don’t forget endpoint protection.
Human error causes 74% of breaches. Use free vulnerability scanners to find gaps. Tools like OpenVAS work well.
For manufacturers, focus on IoT devices. These often get exploited. In finance, check PCI-DSS compliance. Failures lead to big fines.
Once you spot risks, prioritize them. Rank by impact and likelihood. This sets the stage for choosing providers.
Choosing the Right Secure Services Provider
Pick providers with 24/7 SOC monitoring. They need MDR capabilities. Multi-factor authentication integration is key.
Avoid overpaying for wrong fits. Compare costs per endpoint. Expect $5 to $15 monthly. Response times should stay under 15 minutes.
Use a checklist. Verify ISO 27001 certifications. Read client testimonials from your industry. Look for scalable pricing.
A good match reduces setup headaches. It ensures long-term protection. Next, build layers of defense.

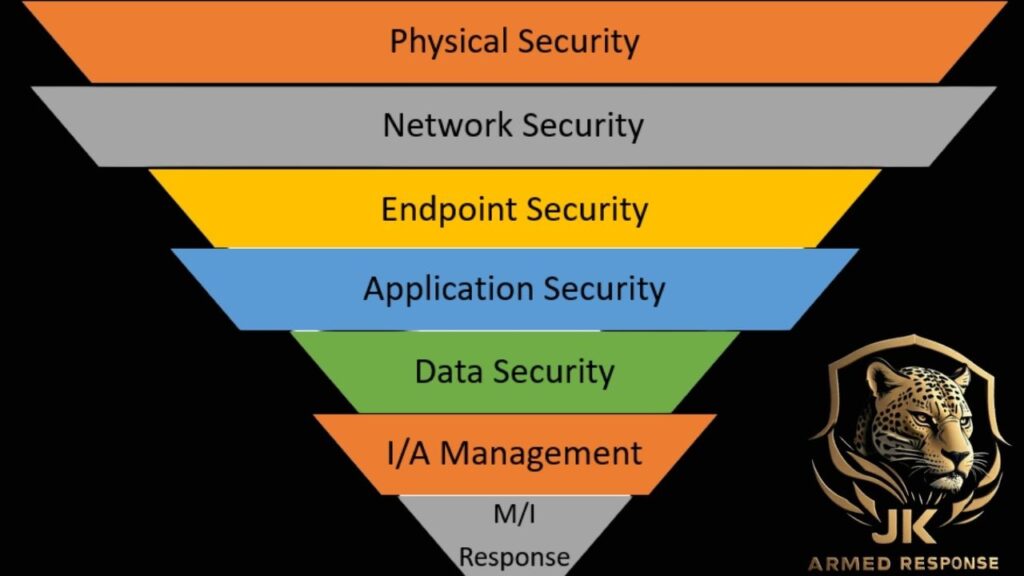
Implementing a Multi-Layered Security Approach
Layer one: Train your team. Run phishing simulations. This cuts click-through rates by 90%.
Layer two: Secure the perimeter. Install firewalls and VPNs. They block 99% of unauthorized access.
Layer three: Protect endpoints and data. Use encryption and DLP tools. Get real-time alerts for odd activity.
Single layers fail often. Integrate step by step. Plan for 2-4 weeks per layer. Test each before moving on.
With layers in place, threats bounce off. But monitoring keeps them at bay. Let’s dive into that.
Monitoring and Responding to Threats
Set up SIEM systems. They log everything. AI spots anomalies fast.
Delayed responses worsen damage. Build incident plans. Include escalation paths. Run drills quarterly.
Track key metrics. Aim for MTTD under 24 hours. Keep MTTR below one hour.
Strong monitoring saves money. It catches issues early. Compliance comes next in line.
Ensuring Compliance and Conducting Audits
Map services to regulations. Use HIPAA for healthcare. FISMA fits government contractors.
Audit failures bring fines. Schedule annual assessments. Create remediation roadmaps.
Include a checklist for cyber insurance. Cover access controls. Classify data properly.
Here’s a sample audit template. Question one: Do you log all access attempts? Question two: Are passwords complex and rotated? Go through 20 such items.
Audits build trust. They show you’re serious. Now, measure the payoff.
Measuring ROI and Long-Term Optimization
Calculate savings first. Factor in avoided downtime. That’s about $8,000 per hour for many SMBs.
Service costs vary. But MDR often delivers 5:1 ROI. Review quarterly to optimize.
Take a mid-sized bank example. They cut breach risks by 60%. Secure services made it happen.
Optimization never stops. Adjust as threats evolve. This keeps your edge sharp.
Conclusion and Next Steps
Secure services handle proactive threat management. They save time and cash for SMBs.
Take action now. Schedule a free risk assessment. Download our customizable playbook.
Stay ahead in cybersecurity. Your business depends on it. For more basics, check cybersecurity on Wikipedia.
Now, let’s expand on some points. After identifying vulnerabilities, explain why IoT risks matter in manufacturing. Devices connect everything. One weak link exposes the network. Hackers exploit firmware flaws. Regular updates fix this.
In finance, PCI-DSS requires card data protection. Secure services automate compliance reports. This avoids manual errors.
When choosing providers, dig into SLAs. Service level agreements detail uptime. Aim for 99.9%. Response guarantees matter too.
For implementation, start small. Pilot one layer. Scale after success. Involve your team early. Buy-in speeds adoption.
Monitoring tools like Splunk or ELK stack help. They aggregate logs. AI reduces false positives. This frees your IT staff.
Incident response plans need testing. Simulate a breach. Time your team’s reaction. Improve weak spots.
Compliance isn’t just checkboxes. It builds customer trust. Audits reveal hidden issues. Fix them before regulators knock.
ROI calculations include soft benefits. Like peace of mind. Or faster recovery times. Use tools like cybersecurity ROI calculators online.
The bank case: They faced phishing waves. Secure services added email filters. Breaches dropped sharply. Revenue stayed steady.
High-risk industries need tailored approaches. Healthcare deals with patient data. Breaches cost $10 million on average per incident, per IBM reports.
Transportation sectors worry about supply chain attacks. Secure services monitor vendors too.
Power grids in utilities face nation-state threats. Layered defenses deter them.
Air traffic control can’t afford downtime. Redundant systems via secure services help.
Overall, secure services evolve. AI integration spots patterns humans miss. Machine learning predicts attacks.
- Stay updated. Attend webinars. Read reports from firms like Gartner.
- Budget wisely. Start with essentials. Expand as needed.
- Employee training ongoing. Monthly sessions reinforce habits.
- Password managers help. They generate strong ones. Reduce reuse risks.
- Backups are crucial. Test restores monthly. Ransomware hits hard without them.
- Cloud security differs. Secure services handle hybrid setups.
- Data classification matters. Label sensitive info. Control access.
- Zero-trust models work well. Verify every request. No assumptions.
- Endpoint detection responds. It quarantines threats automatically.
- Network segmentation limits spread. Isolate critical areas.
- Vulnerability management scans regularly. Patch promptly.
- Third-party risks: Vet vendors. Require audits.
- Cyber insurance covers gaps. But premiums drop with strong security.
- Metrics dashboard: Visualize progress. Share with leadership.
- Long-term: Build a security culture. Everyone’s responsible.
- This approach solves real problems. It protects your bottom line.
If you’re in South Africa and looking for reliable security services for your business, JK Armed Response is the right choice. We operate exclusively in South Africa, providing small to medium-sized businesses with advanced armed response, 24/7 monitoring, and rapid on-site intervention. Visit our website at jkarmedresponse.co.za, book a free risk assessment today, and keep your business protected.
Secure Services: Cybersecurity for High-Risk SMBs
Secure services refer to managed cybersecurity solutions. These protect data, networks, and endpoints from threats. Common threats include ransomware and phishing attacks. SMBs face big risks. In high-risk industries like manufacturing and finance, breaches hit hard. Stats show 43% of cyberattacks target small businesses. Average losses reach $25,000 per incident. This article gives actionable steps. […]



One thought on “Secure Services: Cybersecurity for High-Risk SMBs”