Standard “buzz-in” gates and simple keycards are no longer sufficient to secure high-value properties in Gauteng. In a landscape where criminals are becoming increasingly sophisticated, reliance on standalone security measures leaves critical gaps in your defense. For estate managers and business owners in Johannesburg, the solution lies in complex access control systems—integrated ecosystems that manage entry, analyze data, and communicate directly with armed response units.
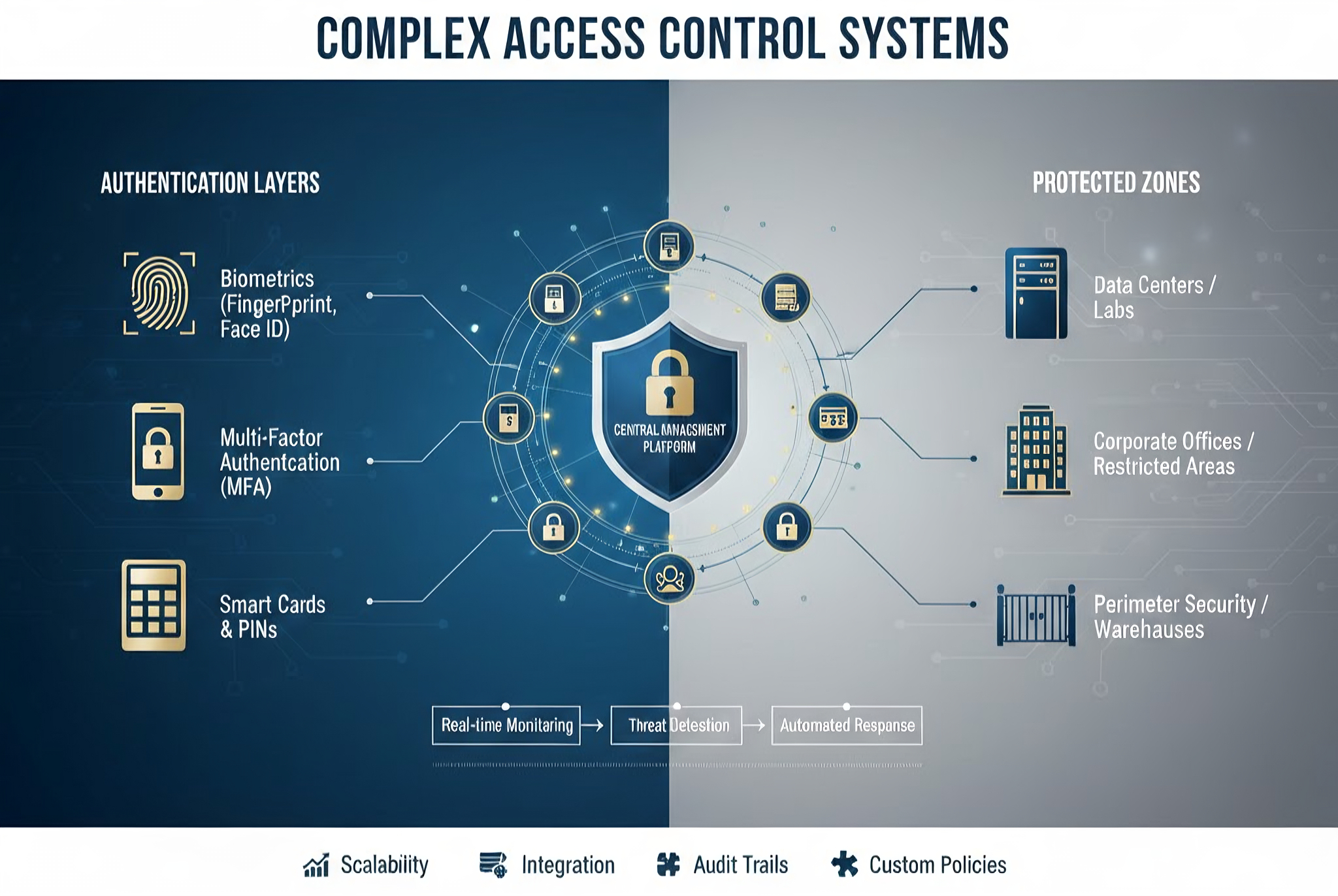
This isn’t about making entry difficult for your staff; it is about making unauthorized access impossible for intruders. A complex system moves beyond the “lock and key” concept. It integrates biometrics, license plate recognition, and cloud management into a single, cohesive shield. When you control who enters, when they enter, and how they are verified, you effectively neutralize 90% of internal and external threats before they escalate.
But technology alone isn’t the silver bullet. It requires intelligent application.
What Makes an Access Control System “Complex”?

A system is defined as “complex” not by its difficulty to use, but by its depth of integration. A basic system asks, “Does this person have a card?” A complex system asks, “Is this person authorized to be here at this specific time, and have they already entered the premises today?”
This distinction is vital for modern security. Complex architectures utilize Multi-Factor Authentication (MFA). For high-risk zones like server rooms or cash offices, a simple card swipe is inadequate. True security requires a “something you have” (access card) combined with “something you are” (biometric fingerprint). This layering ensures that a stolen card becomes useless in the hands of a criminal.
Furthermore, these systems utilize dynamic rule sets. Your main gate might open freely during business hours but automatically switch to strict biometric-only authorization after 18:00. This automation removes the element of human error from your security protocol.
JK Armed Response Specialized Services: Building Your Fortress
At JK Armed Response, we don’t just install hardware; we engineer security logic. Our approach focuses on closing the loopholes that standard installers often miss.
Biometric & Facial Recognition Integration Hygiene and speed are now non-negotiable. We deploy touchless entry solutions that utilize advanced facial recognition algorithms. These systems map facial features in 3D, ensuring that photographs cannot be used to spoof the scanner. For industrial clients, we utilize Biometrics readers capable of scanning through grease or dust, ensuring valid staff are never locked out.
ANPR (Automatic Number Plate Recognition) For residential estates and corporate parks, the vehicle is often the weapon. Our systems link ANPR cameras directly to resident databases. If a vehicle is flagged on a suspicious activity list or has been blacklisted from the estate previously, the boom stays down, and an alert is instantly sent to the control room.

Cloud-Based Mobile Credentials Physical cards are costly to replace and easy to clone. We are shifting South African businesses toward “Phone-as-a-Key” technology using Bluetooth and NFC. This allows facility managers to grant temporary, time-restricted access to contractors or delivery drivers remotely. Once the job is done, the digital key expires immediately.
Solving the South African Problem: Resilience is Key
International security standards often fail in South Africa for one simple reason: the power grid. A standard magnetic lock is only as secure as its power source. When the grid fails, many doors default to an “open” state for safety, leaving your perimeter vulnerable.
The Load Shedding Factor We design our access control nodes with the reality of Stage 6 load shedding in mind. Every JK Armed Response installation includes heavy-duty battery backups and, where necessary, solar integration dedicated specifically to the locking mechanisms. Your security infrastructure must remain online and operational even when the lights go out.
The Human Loophole: Anti-Passback A common breach method is “tailgating,” where an unauthorized person follows an authorized employee through a door. We combat this with anti-passback protocols. The system registers that a user has entered. If that same user credential attempts to enter again (passed back to a friend outside) without first exiting, the system denies access and flags the violation.
The “Armed” Advantage: Integration with Rapid Response
The critical flaw in most IT-installed access systems is isolation. If a door is forced open at 3 AM, a standard system might log an error or perhaps send an email that no one sees until morning. That is not security; that is record-keeping.
At JK Armed Response, we integrate your access control directly with our 24-hour control room. We utilize instant trigger protocols. If a forced door alarm is triggered, it is treated as a priority distress signal. Our operators can immediately view the CCTV feed linked to that specific door and dispatch a response vehicle instantly.
We also implement “Duress Pins.” If a staff member is held at gunpoint and forced to unlock a door, they can enter a specific distress code. The door opens normally to prevent escalation, but a silent panic alarm is simultaneously sent to our armed response team.
Our Installation Process: From Audit to Activation
We do not believe in “box-dropping.” Every site has unique “bleed points” that require a custom strategy.
Step 1: Security Risk Assessment Our senior technicians walk your site to identify vulnerabilities. We look for blind spots, weak perimeter fencing, and high-traffic bottlenecks.
Step 2: Custom System Design We select hardware from top-tier manufacturers like Hikvision, ZKTeco, and Impro, ensuring compatibility with your existing infrastructure.
Step 3: Professional Cabling & Installation We utilize neat, tamper-proof wiring and conduit. A system is only as secure as its cabling; exposed wires are the first target for sabotage.
Step 4: Training & Handover We train your facility manager on how to pull attendance reports, ban users instantly, and manage the system dashboard.
Conclusion
A complex access control system does more than open doors; it secures your business continuity. It simplifies management while complicating the plans of criminals. In the high-stakes environment of South Africa, you cannot afford a passive system. You need an intelligent fortress.
Is your current gate motor your only line of defense? Contact JK Armed Response today for a free site assessment and upgrade your property to the security standard you deserve.
Complex Access Control Systems: Beyond the Keypad
Standard “buzz-in” gates and simple keycards are no longer sufficient to secure high-value properties in Gauteng. In a landscape where criminals are becoming increasingly sophisticated, reliance on standalone security measures leaves critical gaps in your defense. For estate managers and business owners in Johannesburg, the solution lies in complex access control systems—integrated ecosystems that manage […]



One thought on “Complex Access Control Systems: Beyond the Keypad”